Background
The Information Technology Act, 2000 was enacted by the Government of India to grant legal recognition to electronic records, digital signatures, and online transactions in order to facilitate e-commerce and digital governance. It emerged from the need to align with global practices such as the UNCITRAL Model Law on Electronic Commerce and to support India’s growing digital economy. The Act established legal provisions for electronic contracts, cybersecurity practices, and the admissibility of electronic evidence in courts. It also introduced penalties and adjudication mechanisms for cybercrimes including hacking, data theft, and unauthorized access. Overall, the IT Act, 2000 laid the foundational legal framework for India’s digital transformation and continues to be supplemented through amendments and rules to address evolving technological challenges.
Applicability
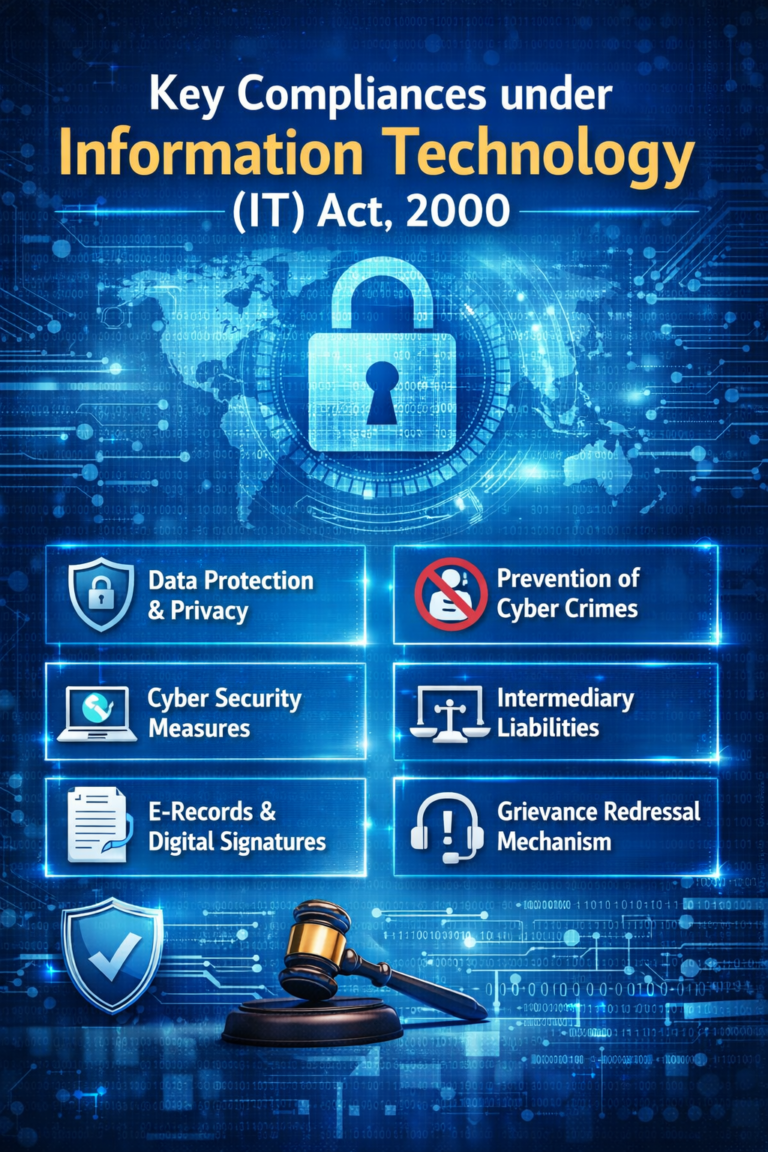
Compliance Requirements under Information Technology Act, 2000
If a law requires documents or records to be retained for a specific period, the requirement is met when they are kept in electronic form, provided the information remains accessible for future reference, the record is preserved in its original or an accurately reproducible format, and it includes details identifying the origin, destination, date, and time of sending or receiving. This does not apply to data generated automatically only to enable electronic transmission. This section also does not apply where a law specifically requires records to be retained as electronic records.
An electronic record shall be attributed to the originator—
(a) if it was sent by the originator himself;
(b) by a person who had the authority to act on behalf of the originator in respect of that electronic record; or
(c) by an information system programmed by or on behalf of the originator to operate automatically.
An electronic record becomes a secure electronic record from the moment a security procedure is applied to it and remains so until it is verified.
Where any security procedure has been applied to an electronic record at a specific point of time, then such record shall he deemed to be a secure electronic record from such point of time to the time of verification.
An electronic signature shall be deemed to be a secure electronic signature if—
(i) the signature creation data, at the time of affixing signature, was under the exclusive control of signatory and no other person; and
(ii) the signature creation data was stored and affixed in such exclusive manner as may be prescribed.
Explanation.– In case of digital signature, the ―signature creation data‖ means the private key of the subscriber.
No person shall knowingly or intentionally conceal, destroy or alter or intentionally or knowingly cause another to conceal, destroy, or alter any computer source code used for a computer, computer programme, computer system or computer network, when the computer source code is required to be kept or maintained by law for the time being in force
Explanation.–For the purposes of this section, ―computer source code‖ means the listing of programmes, computer commands, design and layout and programme analysis of computer resource in any form.
Any person who, without permission of the owner or person in charge of a computer, computer system, computer network or computer resource:
(a) accesses or secures access to it;
(b) downloads, copies, or extracts any data, database, or information, including that stored in removable media;
(c) introduces any computer contaminant or virus;
(d) damages any computer, system, network, data, database, or programs;
(e) disrupts any computer, system, or network;
(f) denies access to any authorised person;
(g) assists anyone in gaining unauthorised access in violation of this Act or its rules;
(h) charges services used by one person to another’s account by tampering with any computer, system, or network;
(i) destroys, deletes, or alters information in a computer resource or diminishes its value or utility; or
(j) steals, conceals, destroys, or alters computer source code with intent to cause damage, shall be liable to pay damages by way of compensation to the affected person.
Penalty & Punishment
Disclaimer: The information contained in this Article is intended solely for personal non-commercial use of the user who accepts full responsibility of its use. The information in the article is general in nature and should not be considered to be legal, tax, accounting, consulting or any other professional advice. We make no representation or warranty of any kind, express or implied regarding the accuracy, adequacy, reliability or completeness of any information on our page/article.